Blog
Security That Ships
Security, strategy, and developer-first thinking for teams pushing open-source forward.
This is some text inside of a div block.

Hopper Just Made Exploitability Verification Instant
Introducing Hopper Exploitability Verification. AI-driven analysis that confirms what is exploitable across your entire software ecosystem. Noise removed. Real impact verified.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

The Real ROI of Function-Level Reachability
With open-source vulnerabilities growing nearly 100% year over year, enterprises need precision. Function-level reachability delivers measurable ROI by eliminating more than 90% of false positives, accelerating remediation, and reducing wasted engineering hours.
Insights
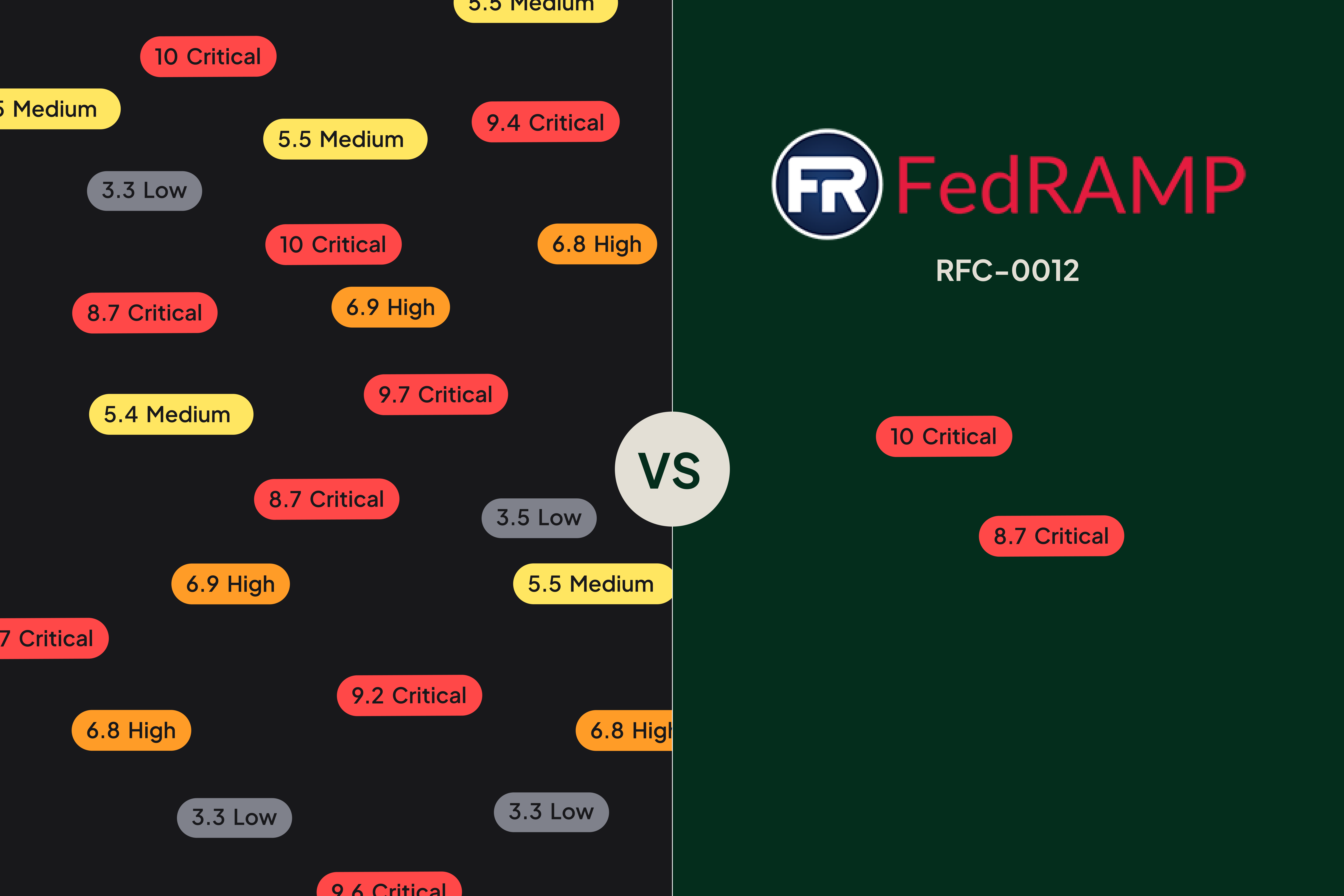

FedRAMP RFC-0012 is Redefining Vulnerability Management Strategy
FedRAMP’s proposed RFC-0012 standard redefines vulnerability management by prioritizing exploitability and automation over traditional CVSS-driven compliance. Learn about major changes, industry reactions, and what executives need to do now to prepare.
Insights
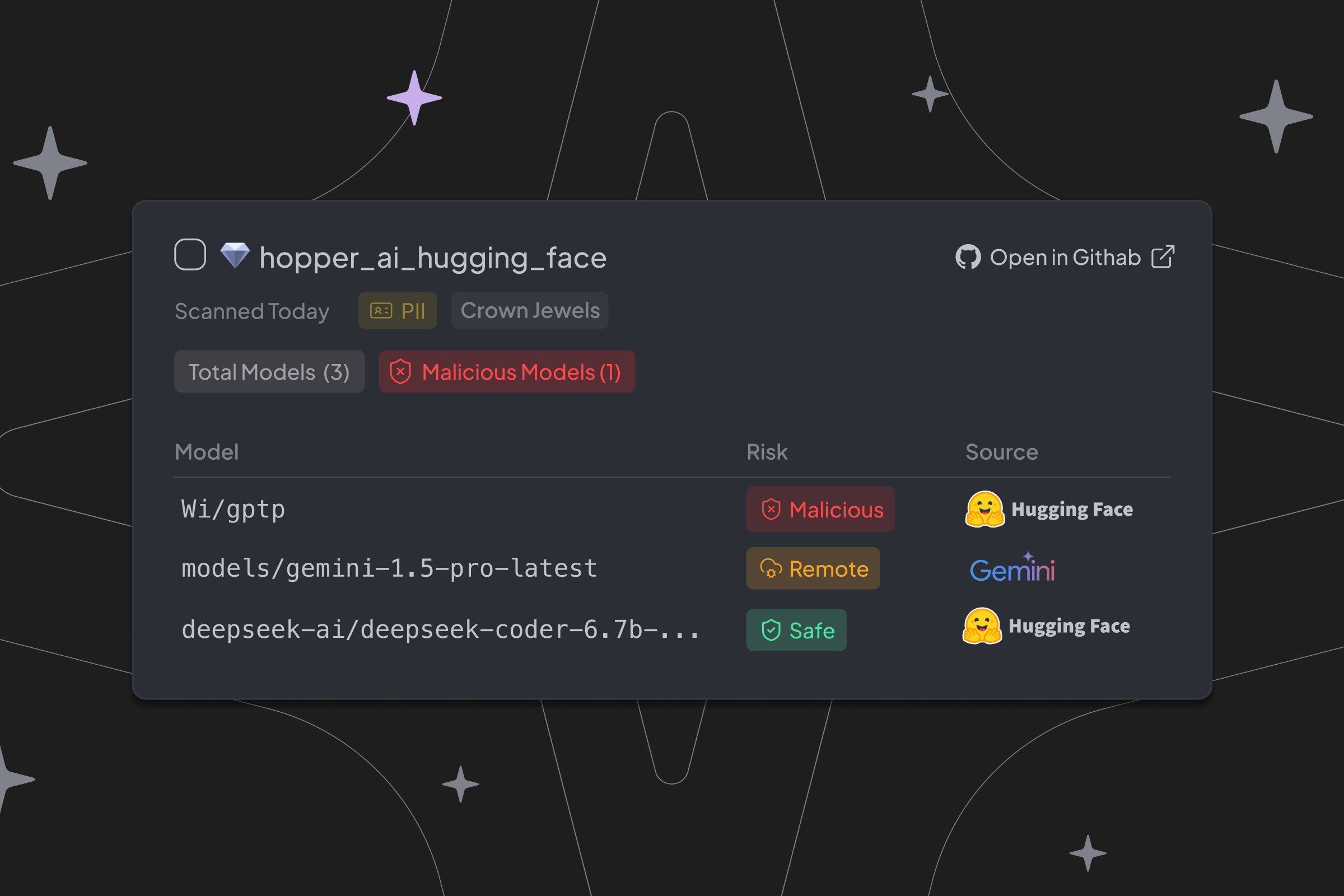

Bringing Visibility to AI Model Usage with Hopper
Hopper’s new AI-BOM and Risk Analysis features give teams full visibility into how AI models and libraries are used across their applications. From embedded models to external APIs, Hopper pinpoints risks like insecure deserialization, data exposure, and compliance violations, delivering actionable insights with zero friction.
Product


Quieting the Noise from the Start, with Thoughtful Branding and Design
Hopper’s branding and product design are built around one principle: cutting through noise to create clarity in open-source security. From typography and color to product workflows and AI cues, every detail is designed to reduce distractions, build trust, and help teams focus on what truly matters.
Product
.png)

From 134 Vulnerabilities to 3 Real Risks: How Hopper Cuts Through the Noise
Hopper transforms vulnerability management by reducing noise and focusing teams on real risk. In this demo, a Python app with 134 vulnerabilities is distilled to just 3 critical issues worth fixing through function-level reachability and EPSS.
Insights
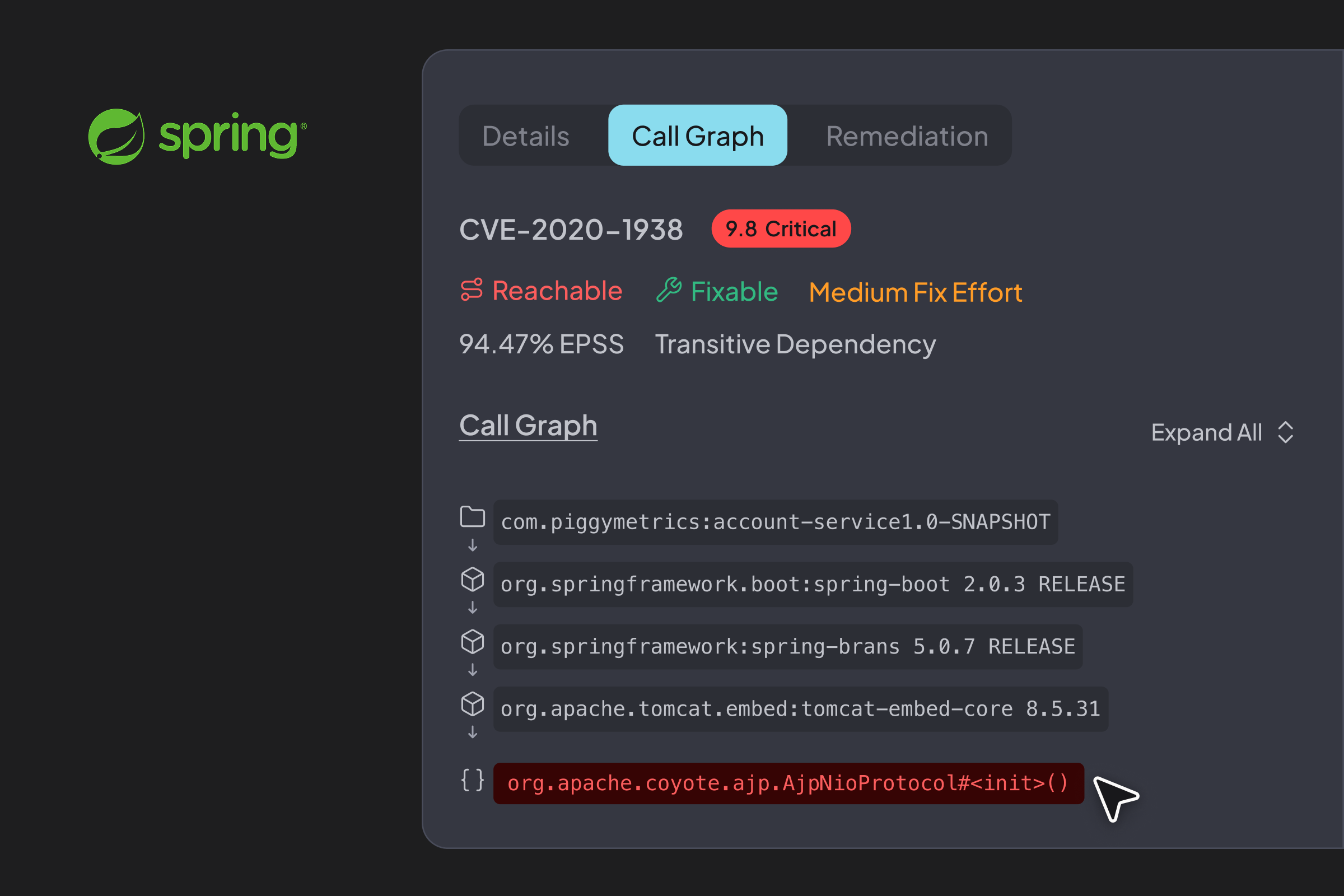

How Hopper Supports Evidence-Based Vulnerability Scanning for Spring Applications
Spring’s dynamic features break traditional static analysis. Hopper delivers the first and most accurate production-aware call graph analysis for Spring, modeling behaviors like reflection, proxies, and spring.factories for unmatched accuracy and fewer false positives.
Product
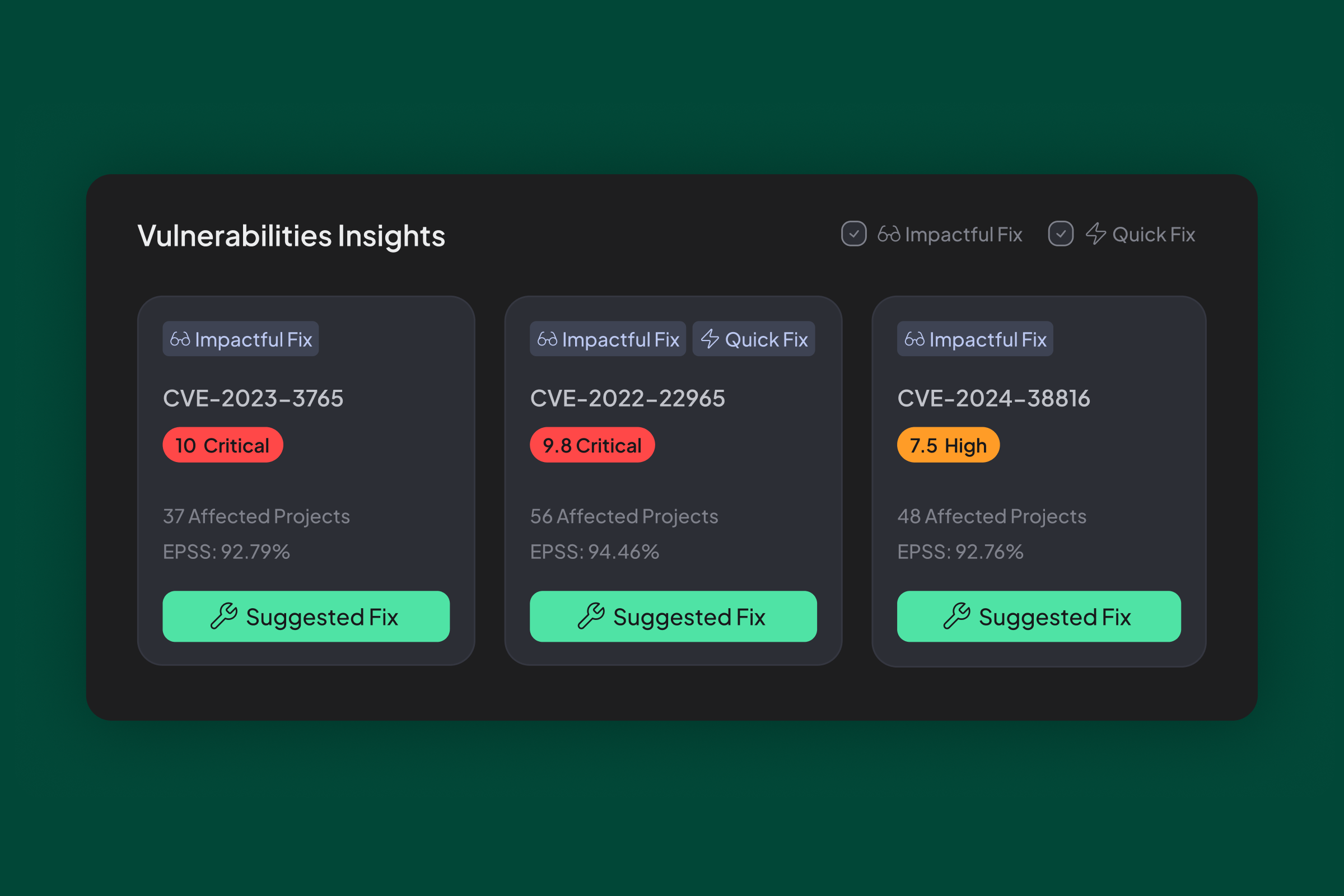

Introducing Vulnerability Insights: Cutting Through the Noise of Monorepos
Hopper cuts through the noise of monorepo dependencies by identifying and surfacing root causes, enabling security teams and developers to triage issues faster and more effectively.
Product
.png)

Reducing Risk, Accelerating Innovation: Lessons from Hopper Customers
HPE, Mesh Payments, and a Fortune 500 enterprise transformed their open source security with Hopper, cutting vulnerability noise by up to 99%, saving millions, and accelerating remediation.
Insights

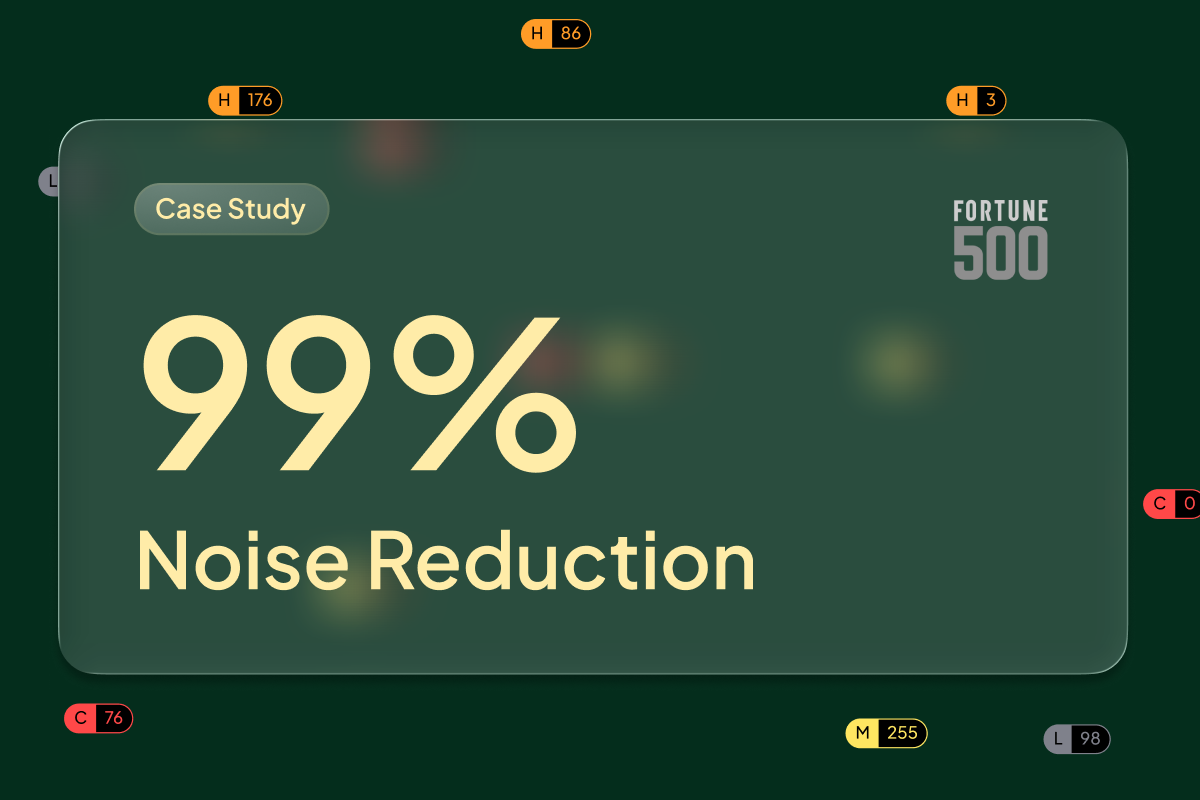
Fortune 500 Org Cuts Vulnerability Noise by 99% with Hopper
Fortune 500 Org Cuts Vulnerability Noise by 99% with Hopper
A Fortune 500 company partnered with Hopper to transform its vulnerability management strategy. By leveraging function-level reachability and exploitability scoring, the company achieved a 99% reduction in open-source vulnerability noise and identified actively exploitable risks missed by their incumbent tool.
Customer Stories
Newsroom
Hopper Press Mentions and Releases
Visit Publication Article

September 15, 2025
In Praise of Resilience: Why We Invested in Hopper Security
-Logo.wine.png)
Visit Publication Article

September 4, 2025
The ART of Taming Agents: A CISO’s Framework for Managing Enterprise Risk in the Age of Agentic AI

Visit Publication Article

April 25, 2025
Hopper Uncovers Over 2.5 Million Vulnerabilities Hidden in Java

Visit Publication Article

April 22, 2025
Hopper raises $7.6M to accelerate software development with streamlined risk management
Visit Publication Article

April 22, 2025
Open Source Security Firm Hopper Emerges From Stealth With $7.6M in Funding

