Spring is powerful, but with that power comes a great deal of complexity. Hopper delivers the first accurate vulnerability analysis for Spring applications, modeling dynamic behaviors like reflection, proxies, spring.factories, and annotation-driven wiring that traditional tools cannot see.
The result is the most accurate call graphs available for Spring applications, with fewer false positives and actionable security findings you can trust.
Modern Java Applications Deserve More Than Textbook Static Analysis
Spring revolutionized enterprise Java development with dependency injection, annotation-driven routing, and modular auto-configuration. But these features come at a cost: they obscure the true structure and flow of the application, especially from the perspective of static analysis tools. This is exactly where Hopper’s accuracy sets it apart.
Static tools were built for predictable code. But Spring apps are anything but static:
- Beans are injected dynamically, not instantiated explicitly.
- Routing is declared through annotations, not centralized tables.
- Proxies intercept method calls before they reach business logic.
- Reflection powers registration and bootstrapping behind the scenes.
If your analysis tool cannot model this behavior, your vulnerability scan is not just incomplete, it is misleading. Hopper’s modeling closes that gap.
Why Traditional Tools Get Spring Wrong
Building a precise call graph in Spring is notoriously hard. Here’s why:
Dependency Injection & IoC
Spring applications delegate object creation to the container. @Autowired fields do not tell you which class is injected, and only runtime resolution can answer that. Static tools stop short, resulting in missing or incorrect connections.
Annotation-Based Routing
Controllers and request mappings (@RestController, @RequestMapping, etc.) define application entrypoints, but they are discovered at runtime by Spring. Without modeling the routing engine, static tools cannot reliably identify exposed endpoints.
Proxies & AOP
Spring uses dynamic proxies for transactions, caching, and more. Tools that don’t recognize these proxies will:
- Miss the actual method being invoked
- Misattribute behavior to the proxy class
- Break the flow of the call graph
Reflection Everywhere
Spring relies heavily on reflection to instantiate beans, scan the classpath, invoke methods, and bind data. These dynamic behaviors do not show up in traditional ASTs or call hierarchies.
spring.factories and Auto-Configuration
Spring Boot bootstraps functionality through spring.factories, loading components like ApplicationContextInitializers, AutoConfiguration classes, and listeners via classpath scanning. These components often initialize entire subsystems, with no direct references in source code.
The Result: Broken Call Graphs and False Positives
When traditional static tools attempt to scan Spring applications for vulnerabilities without understanding its internals, their analysis is flawed. They often:
- Miss key execution paths entirely, leaving real vulnerabilities undetected
- Surface unreachable code as exploitable, creating false positives
- Overestimate security risk from transitive dependencies that are never called
- Fail to identify the true attack surfaces that matter in production
- Lack the call graph evidence developers need to remediate issues with confidence
In a security workflow, this means noisy vulnerability alerts, wasted triage effort, and dangerous gaps where reachable or exploitable code is missed. Hopper’s precision eliminates these pitfalls, giving teams accurate, actionable findings they can trust.
Hopper Understands Spring Internals
Hopper is built for real-world applications, not textbook examples. Our analysis engine is purpose-built to model dynamic behavior in systems like Spring. Hopper handles the constructs other tools ignore:
- Bean resolution via
@Autowired,@Service,@Configuration, and constructor injection - Annotation-driven controllers and routing logic
- Classpath discovery and
spring.factories-based bootstrapping - Reflection-powered method calls and type resolution
We don’t guess, we trace, with a focus on unmatched, accurate reachability analysis.
When analyzing Spring, Hopper:
- Understands and interprets
spring.factories-based auto-configuration to reveal which components are activated during application startup. - Resolves active beans based on the environment, excluding unreachable paths
- Understands the full Spring Boot lifecycle, from
main()toApplicationContextto active controllers - Accurately identifies entrypoints based on real route mappings, not static strings
Spring Boot Application Reachability Analysis
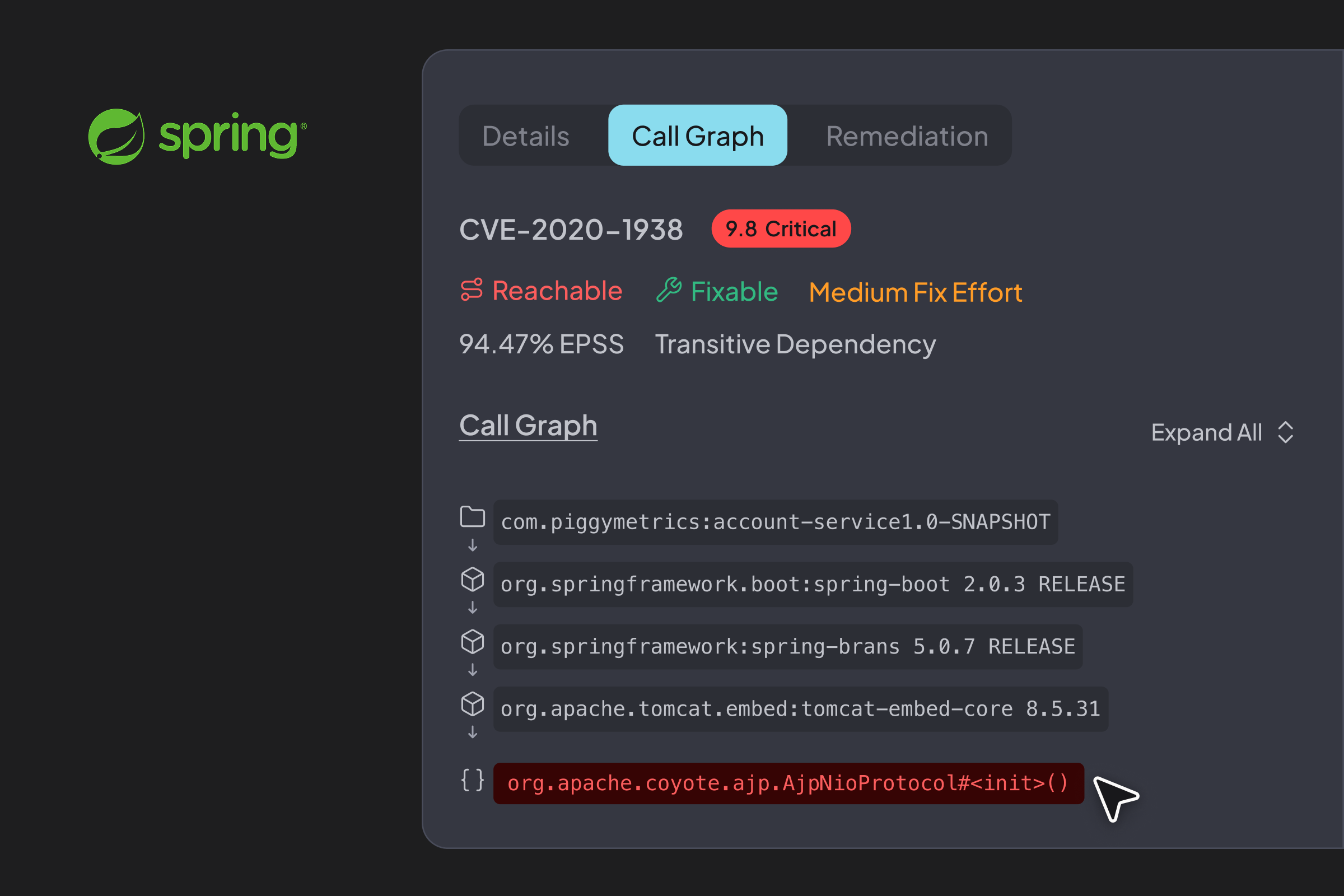
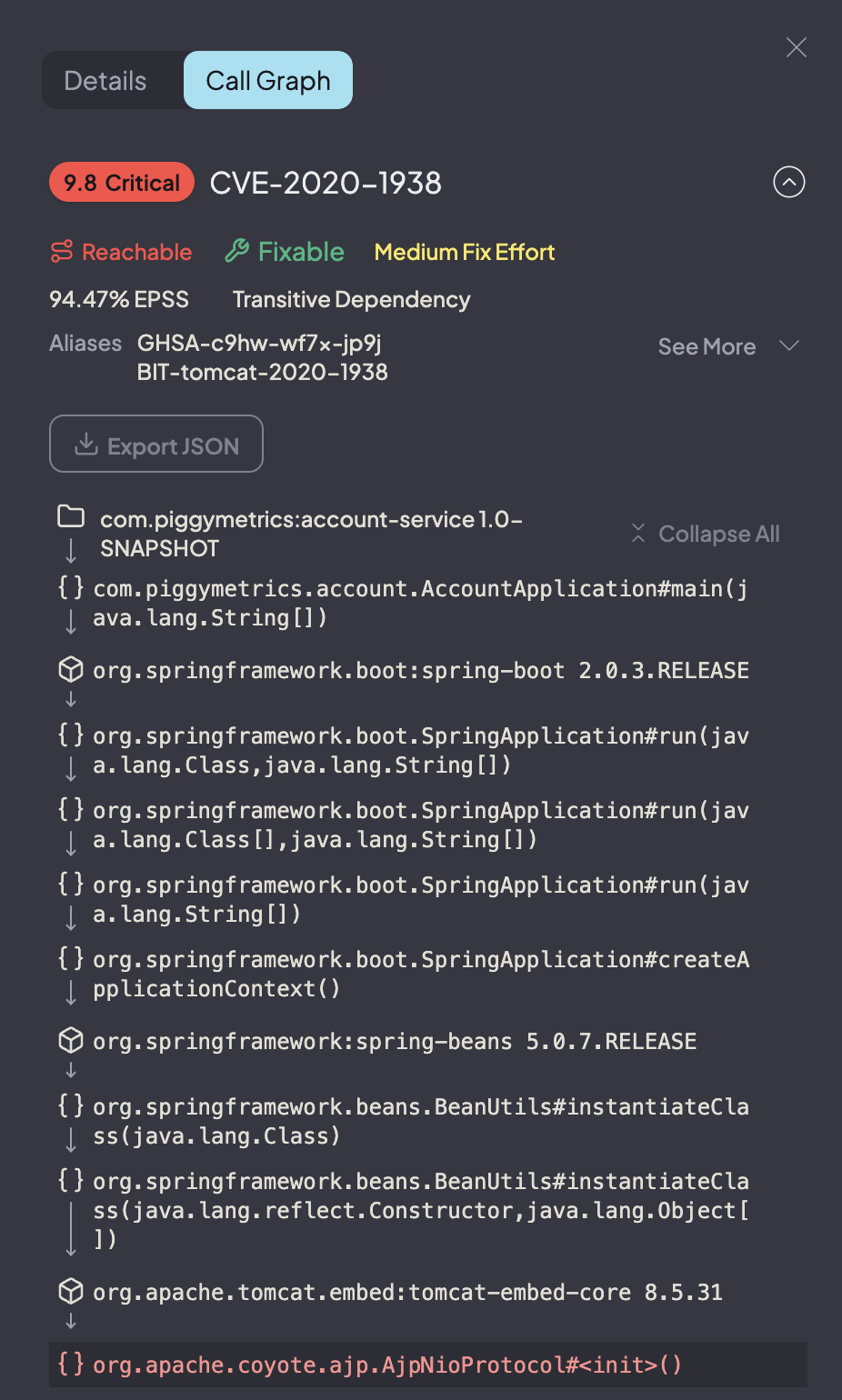
Here’s a call graph generated by Hopper for a real Spring Boot app.
It shows execution from main() into Spring Boot internals, tracing across dynamic class loading, spring.factories, and even reflection-based instantiation. It even shows the auto-configuration of the embedded Tomcat AJP connector:
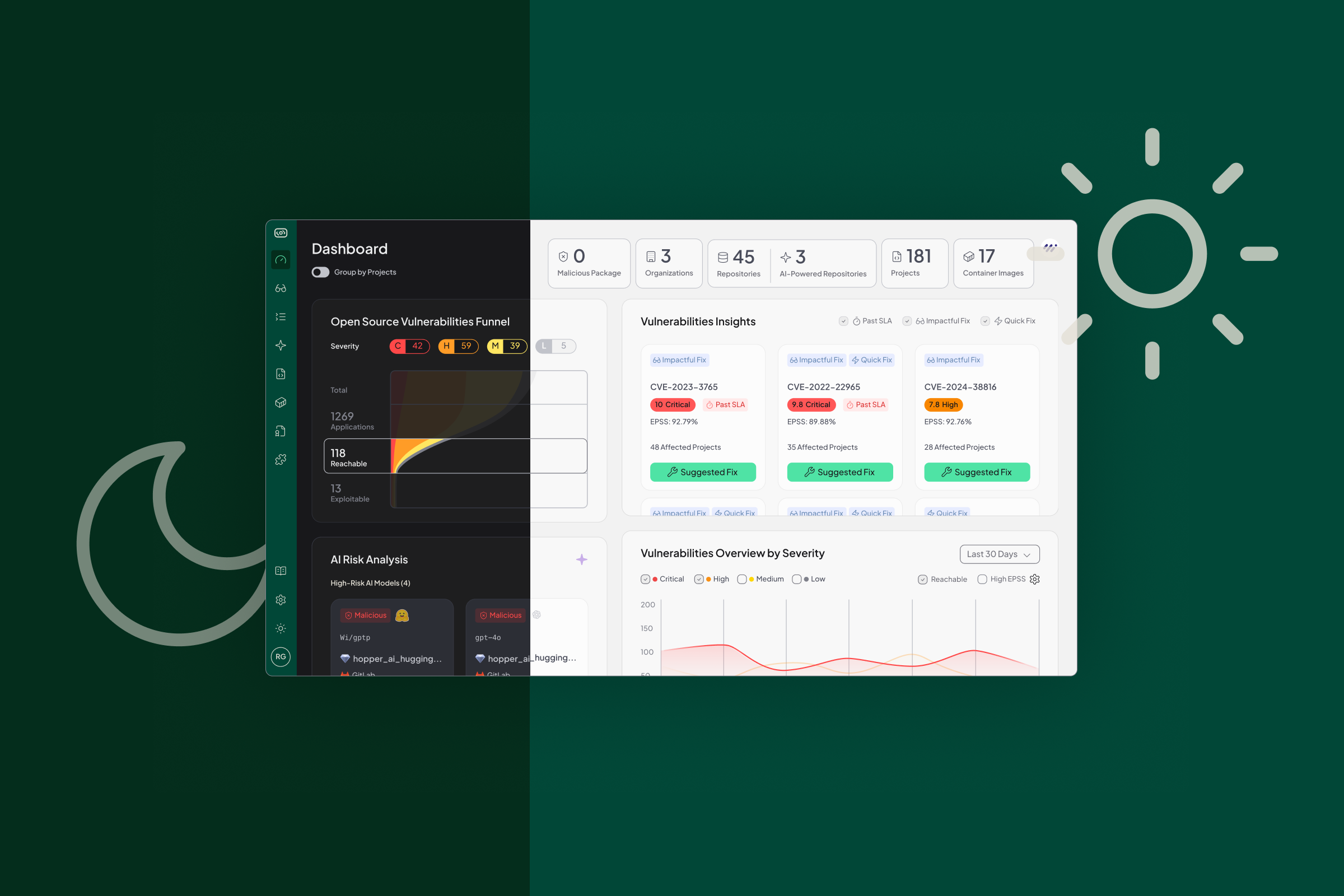
Actionable Results, Not Overwhelming Alerts
Instead of flagging every vulnerability in your dependency tree, Hopper tells you:
- Which functions are actually reachable
- Whether a vulnerable method is truly exposed through an active route
- What logic is invoked in the application’s active configuration, not just what exists in your codebase
This means:
- Less noise, more signal
- Real vulnerabilities aren’t missed
- Clear prioritization based on actual reachability
Understand the True Security Posture of Your Spring Application
Spring gives developers abstraction and power, but those same abstractions break conventional static analysis. With Hopper, you do not just scan your code, you understand your application’s true behavior in context, with the most accurate call graphs in the industry.
Hopper brings precision and clarity to even the most complex Spring environments, so your team can focus on fixing what matters, not sifting through noise. See Hopper in action and discover how accurate call graph analysis can transform your security workflow.