The Real Cost of Too Many Alerts
For most organizations, the biggest challenge in application security isn’t tool coverage, it’s clarity. Security teams are flooded with alerts, developers are asked to fix issues that may never be exploited, and business leaders are left questioning whether time and resources are being directed toward the risks that actually matter. The result is wasted engineering effort, slower release cycles, and lingering doubt about whether the company is truly reducing its exposure.
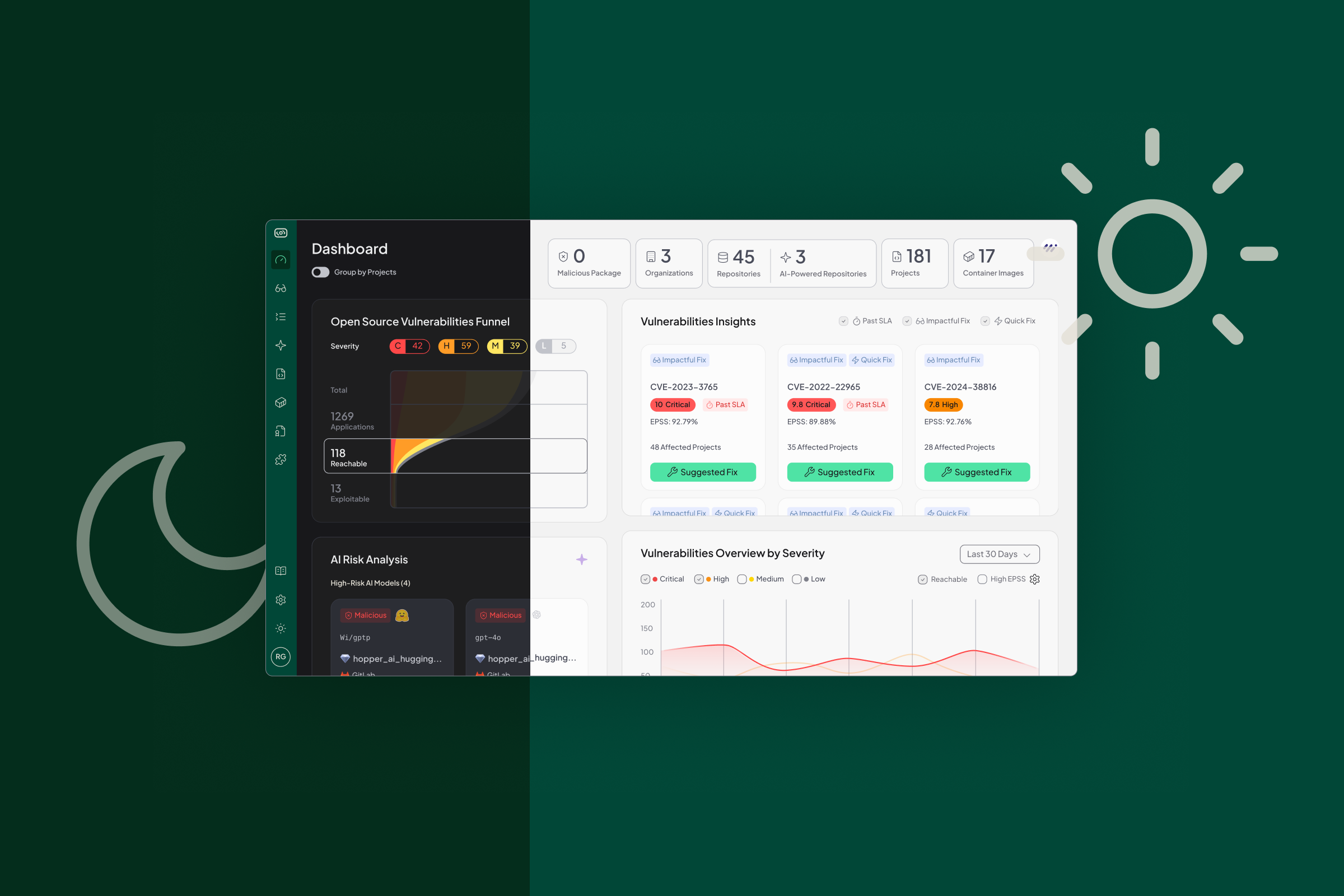
Hopper addresses this gap by giving teams precision. Instead of drowning in hundreds of theoretical vulnerabilities, security leaders can focus on the handful of issues that are both exploitable and high-risk. Developers get the evidence they need to trust the findings, down to the line of code in GitHub, which accelerates fixes rather than slowing them down.
At the leadership level, this means less wasted spend on security firefighting, faster mean-time-to-remediation, and a clear story for auditors, regulators, and customers. Security becomes a business enabler instead of a bottleneck.
Here’s how Hopper makes that shift real in practice. In just a few minutes, we show how Hopper takes a Python application with 134 vulnerabilities and distills it to 3 real risks worth acting on.
Step 1: Move Beyond Inventory Lists
Most tools show you a flat list of projects and manifests. Hopper lets you pivot into the application view, where risk is mapped to how your applications actually function.
Step 2: Filter for What’s Reachable
In our example, the Python application shows 134 vulnerabilities, 84 of them critical or high severity. Rather than stopping there, Hopper applies function-level reachability analysis to reveal which vulnerabilities are actually exploitable in context.
Step 3: Cross-Reference with EPSS
Not all vulnerabilities carry equal likelihood of exploitation. By layering in Exploit Prediction Scoring System (EPSS) data, Hopper shows which reachable issues have meaningful exploit probability. With just two filters (reachability and EPSS), we reduced 134 findings to 3 that matter.
Step 4: Trace the Evidence Trail Back to Code
For each prioritized vulnerability, Hopper provides a full call graph from entry point to vulnerable function. Every line of code is linked directly back to GitHub, so developers can see exactly where the issue originates and remediate with confidence.
From Alert Fatigue to Actionable Security
This demo isn’t just about filtering vulnerabilities, it’s about changing how organizations think about risk. By focusing on what’s reachable and exploitable, Hopper cuts through the noise and helps teams act with precision. Security leaders gain confidence that their resources are protecting the business, developers get clarity on what to fix and why, and executives see security accelerate rather than slow down product delivery.
This is the shift from reactive alert fatigue to actionable security, and it’s what makes Hopper different. It’s how organizations can finally align security priorities with business outcomes.

.png)