Trace And Fix Every
Exploitable Vulnerability in
Exploitable Vulnerability in
|
Use AI agents and function-level traces to confirm exploitability, prioritize action, and accelerate response across every application you build, buy, or use.
Start Free Today
30 days free. No credit card required. Includes 5 container scans.
How Hopper Transforms Vulnerability Response
Prove What’s Exploitable
Combine function-level traces with AI reasoning to investigate and validate impact.
Accelerate Response
Identify affected assets instantly, publish advisories faster, remediate with ease, and meet customer commitments.
Respond Across Every Artifact
Analyze and protect binaries, containers, and repositories, across every application your business builds, buys, or uses.

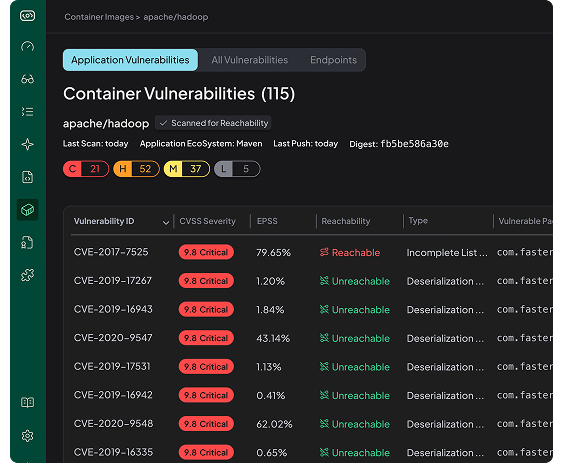
Container Image Analysis
Application-Layer Vulnerabilities detected in commonly used public container images.
View All Containers
rundeck/rundeck:5.16.0
Digest:
sha256:66227d7fc48c632efc3cf55b92065c779f3d16743f4b4564be9e597d54385d91
Application Vulnerabilities
C
2
H
17
M
24
L
2
Reachable Vulnerabilities Only
C
0
H
2
M
10
L
2
↓
68.9
Noise Reduced
apache/rocketmq:latest
Digest:
sha256:a6976cd5841facfda294616a0b8797e7f41fa0292d51ad4e46b2ff224ce64995
Application Vulnerabilities
C
0
H
9
M
12
L
2
Reachable Vulnerabilities Only
C
0
H
3
M
5
L
0
↓
65.2
Noise Reduced
library/zookeeper:3.7
Digest:
sha256:3e840492fc776f8853149b70ad9f8b698b7e640323d2757aa4f8d595812e8fe2
Application Vulnerabilities
C
0
H
2
M
6
L
0
Reachable Vulnerabilities Only
C
0
H
1
M
2
L
0
↓
62.5
Noise Reduced